

Is SERO affected by Zero Knowledge Proofs Infinite Counterfeiting Vulnerability?
In last few weeks we had received many queries regarding how SERO plans to fight the zero knowledge proofs infinite counterfeiting vulnerability and is it even affected at all. Although the SERO team did communicate with community members individually but with the recent happenings the team decided to publish an official article about the same.
What is Zero Knowledge Proofs Infinite Counterfeit Vulnerability?
In March 2018, Zcash team members found out a deadly vulnerability in the underlying cryptography zero knowledge proofs which could allow attackers to secretly print infinite amount of Zcash currency without the knowledge of core team.
“The vulnerability had existed for years but was undiscovered by numerous expert cryptographers, scientists, third-party auditors and third-party engineering teams who initiated the new projects based upon the Zcash code,” they stated. “Discovery of the vulnerability would have required a high level of technical and cryptographic sophistication that very few people possess”
Why is SERO not affected by infinite counterfeiting vulnerability?
Now since a part of SERO protocol is also based on the same underlying cryptography, Zero knowledge proofs it might make you question whether SERO is resistant to this vulnerability or not.
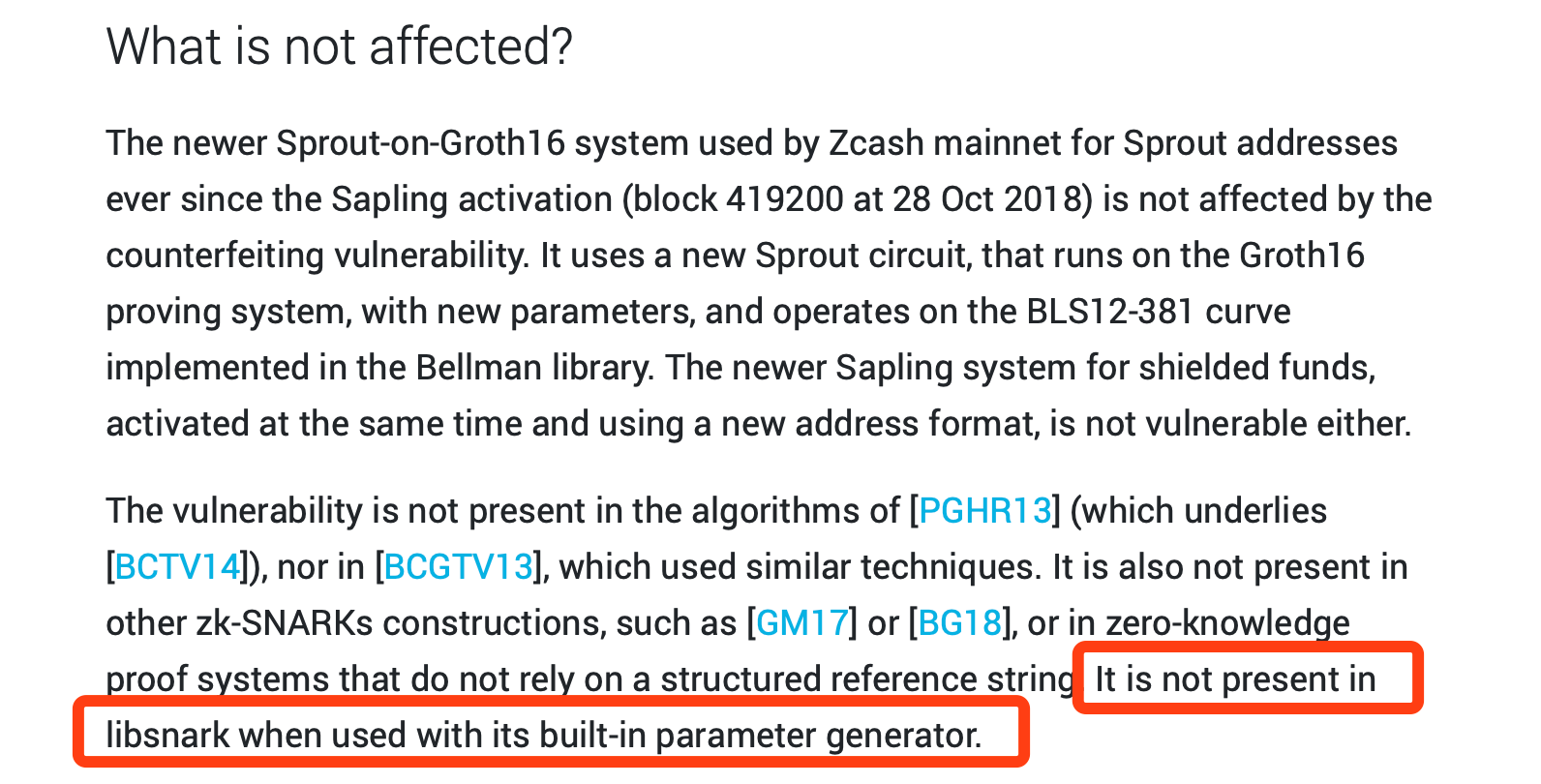
The reason SERO is not affected is because we use the Sprout-on-Groth16 proof system, and also the libsnark built-in parameter generator.
This can be verified in the latest official statement released by Zcash team about the infinite counterfeit vulnerability.
Resource : https://z.cash/blog/zcash-counterfeiting-vulnerability-successfully-remediated/
Also for those community members who are not aware, SERO team actually improved the earlier encryption library and created a new and faster one called “SUPER-ZK” which enabled SERO team to achieve 20 times faster encryption against the Zcash’s zk-snarks code during the SERO testnet.
You can verify the code and version in this video that SERO team released back in 2018.
SERO vs Zcash encryption demonstration video : https://www.youtube.com/watch?v=bc6yHTLSl5M
Will the SERO team reveal the Sprout-on-Groth16 part of code to public?
“This part of code is not made public as of yet but we have always believed that blockchain technology must be open source. and hence the Groth16 part of code will be made available for public when main network goes online ” said SERO co-founder and chief architect Mr Gordon.
The SERO community is growing stronger and with the current BetaNet mining along with upcoming updates we can assure our community that
the journey has just begun, irrespective of the market conditions the SERO team will continue to work hard and develop a true privacy protection platform for decentralised applications that supports Turing complete smart contracts.
Related news
Search news
Recommended news
Super Zero Protocol (SERO) Smart Contracts Tutorial — Issue Anonymous Tokens
2019-05-21
SERO Privacy — Use Cases
2019-05-15
SERO VS Zcash : A comparative analysis
2019-03-31
Is SERO affected by Zero Knowledge Proofs Infinite Counterfeiting Vulnerability?
2019-02-08
Data Privacy Protection and Blockchain
2019-01-17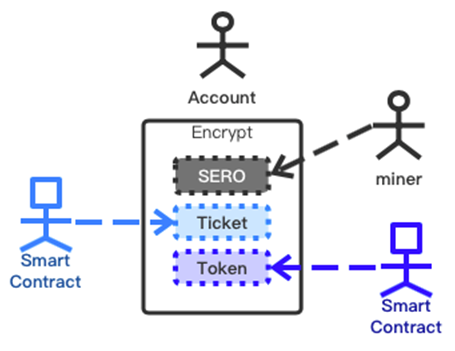
SERO — The Technological Innovation in the Blockchain Privacy Protection
2018-12-17
Privacy Protection and Blockchain
2018-12-15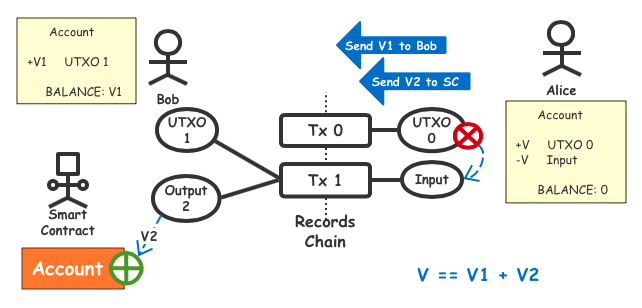
Super Zero Protocol (SERO) Smart Contracts Anonymous Tokens Issuance Principle
2018-12-04