

Privacy Protection and Blockchain
As the title suggests,this article will be focused on privacy protection and blockchain and how both of these are related.This article assumes some level of knowledge about blockchain principles but assumes little knowledge of data protection and privacy.
So we’ll address the key information via bit topics and will cover the concepts from basic and forth.

What is a blockchain?
Blockchain is a type of distributed ledger,comprised of digitally recorded data in packages called blocks which are linked together in chronological order in a manner that makes the data very difficult to alter once recorded, without the alteration of all subsequent blocks and a majority of the network colluding together. Each node on the network (generally) contains a complete copy of the entire ledger, from the first block created — the genesis block — to the most recent one. Each block contains a hash pointer as a link to a previous block, a timestamp and transaction data.
What is a Smart Contract?
Smart contracts use blockchain technology. The term is used to describe computer program code, maintained on the various “nodes” constituting a blockchain network that is capable of facilitating, executing, and enforcing the negotiation or performance of an agreement upon the occurrence of predefined conditions.The smart contract code executes on each node and the resulting output is stored on the blockchain. Where “tokens” of value are involved, the smart contract code can also automatically transfer these tokens (and underlying value), thus effectively enforcing the outcome of the smart contract code.
Do blockchains process personal data?
‘Personal data’ is any information relating directly or indirectly to a ‘living natural person’, whether it actually identifies them or makes them identifiable.The nature of the public blockchain means that every transaction taking place will be published and linked to a published public key that represents a particular user. That key is encrypted so that noone who views the blockchain would be able to directly identify the individual or corporate entity that represents the user.
However, the re-use of the public key enables individuals to be singled out by reference to their public key, even if they cannot be directly identified.When the public key is visible, it could be possible to attain information that enables an individual to be identified, either because it is held by the service provider or because someone is able to connect a public key to an individual or organisation, (for example, through their IP address or its connection with a website). At that point, all transactions that the relevant individual has made are publicly available.
Encrypted personal data can often still be traced back to a person if enough effort is put into it by experts or someone holds the key to decryption. Therefore, encrypted data will often qualify as personal data and not as anonymous data. This means that in most instances the privacy rules will be applicable to at least some of the data involved in blockchain systems.
Variety of blockchain systems
1) Private vs. Public blockchains
2) “Off-Chain”
3) “Sidechains”
4) Non-Permissioned vs. Permissioned Blockchains
5) Hyperledger
6) R3
7) Zero Knowledge Proofs
Analysis of the different Blockchain systems.
Understanding the data on a traditional (Bitcoin/Ethereum) blockchain
On each block of the blockchain there are two types of data: 1) a header that includes a date stamp, the identity of the source of the data (an address), and the previous block’s header hash, called ‘the pointer’; and 2) the payload, which is the data to be stored.
The header is not encrypted, only the payload is normally encrypted. The hash in the header is of earlier blocks to create the immutable chain of blocks. The payload is generally a description of the document (metadata) and the hash representing the actual document.
A smart contract would operate as follows: when X wants to upload a new document description to the blockchain, the smart contract will create a transaction by combining a description of the document and its hash to form a payload and add a header. The header plus payload equals a transaction and a validated transaction equals a block. Upon validation of the block, the smart
contract would then send the document itself to the Y database system for storage. We assume that the Y database is off the blockchain and has limited access through the use of passwords which can be time sensitive. The blockchain transaction will be proof that the document was uploaded at a given time, and anyone will be able to verify that the document held in the
off-chain database is the same document as the one referred to in the blockchain transaction.
Understanding the data on new blockchain technologies
As mentioned above, some technologies permit a greater degree of anonymity.
Whether the degree of anonymity satisfies European standards under the CJEU’s Breyer decision and the Article 29 Working Party Opinion is another matter. For example, Dash encrypts public keys. While new blockchain technologies using zero knowledge proofs — can verify transactions without details of the transaction itself. However, the work involved developing a proof is extensive and has significant computation costs. As a result, there are scalability challenges with these tools.
Blockchain data protection and Privacy impact assessments
Under the GDPR a data protection impact assessment is required for processing, which is likely to present a high risk to the rights and freedoms of natural persons. Blockchain projects can be roughly divided into three categories:
– Specialised blockchain systems designed to process essentially non-personal
data, such as bills of lading, letters of credit, or diamond certificates;
– Specialised blockchain systems designed to process personal data, such as proof of identification, or even sensitive personal data such as medical records;
– Non-specialised blockchain systems that can be used to process any form of data.
Non-specialised blockchains are likely to put the onus of compliance on the users themselves, through terms of use that:
a) prohibit posting of certain kinds of personal data; and
b) require users to have consent or another legal basis for processing.
The data protection impact assessment will need a robust technical analysis to show that the security of the system is at least as robust, if not more robust, than traditional cloud-based systems.
Related news
Search news
Recommended news
Super Zero Protocol (SERO) Smart Contracts Tutorial — Issue Anonymous Tokens
2019-05-21
SERO Privacy — Use Cases
2019-05-15
SERO VS Zcash : A comparative analysis
2019-03-31
Is SERO affected by Zero Knowledge Proofs Infinite Counterfeiting Vulnerability?
2019-02-08
Data Privacy Protection and Blockchain
2019-01-17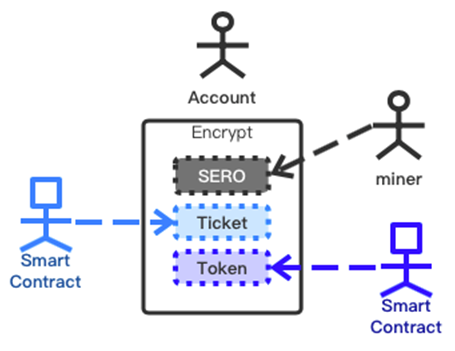
SERO — The Technological Innovation in the Blockchain Privacy Protection
2018-12-17
Privacy Protection and Blockchain
2018-12-15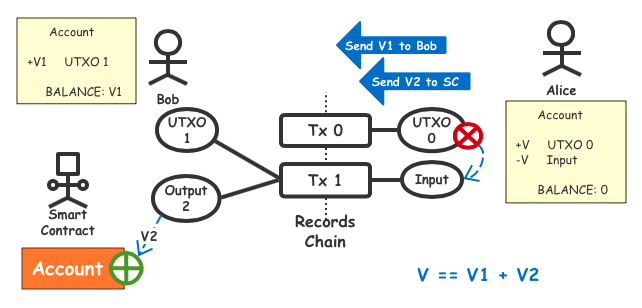
Super Zero Protocol (SERO) Smart Contracts Anonymous Tokens Issuance Principle
2018-12-04